Computer
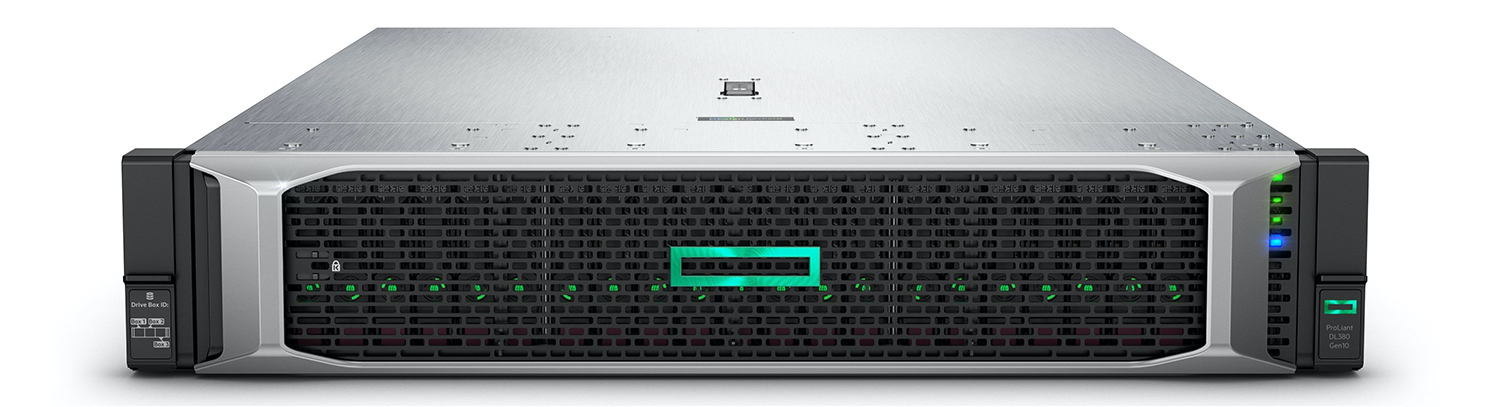
The endpoint that requests access — workstations, servers, IoT devices, and services. Each computer is an actor in the network, not an implicit member of a trusted zone.
Zero Trust · AI Identity
CanID — Computer Automated Network ID — delivers AI-powered identity management for software-defined networks. In a Zero Trust architecture, intelligence never grants access simply because a device sits inside the perimeter.
About CanID
CanID builds the bridge between automated network infrastructure and intelligent access control. We help organizations move beyond perimeter-based security — where presence on a LAN implied trust — toward architectures where every request is authenticated, authorized, and continuously evaluated.
Our platform treats identity as the primary signal: who is connecting, which device is involved, what context applies, and whether current behavior still matches policy. Network segmentation, automation, and data-flow rules all follow from that single source of truth.
In a CanID-protected network, AI does not trust a computer blindly just because it is on the network. Every endpoint earns access — moment by moment.
The name
Three concepts — Computer, Automated Network, and Identity — define how we design, secure, and operate infrastructure for the next generation of connected systems.
The endpoint that requests access — workstations, servers, IoT devices, and services. Each computer is an actor in the network, not an implicit member of a trusted zone.
A network steered by software, rules, and policy — not manual wiring alone. Segmentation, routing, and enforcement adapt dynamically as identity and risk change.
The digital fingerprint of users, devices, and workloads. Identity drives access, segmentation, and automation according to who or what is connecting — not merely where.
Security model
Zero Trust assumes breach. No user, device, or service receives implicit trust based on network location. CanID embeds this philosophy into identity workflows and automated policy enforcement.
How it works
CanID connects computers, network infrastructure, and identity into one continuous trust loop powered by artificial intelligence.
An endpoint requests access to resources. Its hardware profile, certificates, and runtime state become part of the trust evaluation.
The infrastructure that routes and controls data flow. Policies enforce segmentation and micro-perimeters aligned with identity context.
A digital fingerprint for users, devices, and services. Identity binds authentication to authorization and drives automated responses.
Inventory endpoints and map them to identities across the automated network.
AI evaluates trust signals — behavior, posture, and policy compliance in real time.
Apply least-privilege access and dynamic segmentation at the network layer.
Continuously adjust trust as context changes — without blind perimeter assumptions.
Whether you are designing a Zero Trust roadmap or operationalizing software-defined segmentation, CanID helps you put identity at the center of every connection.